Containers
-
Containerization is a lightweight alternative to full machine virtualization.
-
It involves encapsulating an application into a single, isolated operating environment, packed with all the files, libraries, and dependencies it needs to operate.
-
By combining these elements into one unit, the application can run consistently across different platforms and environments.
How Containers Work
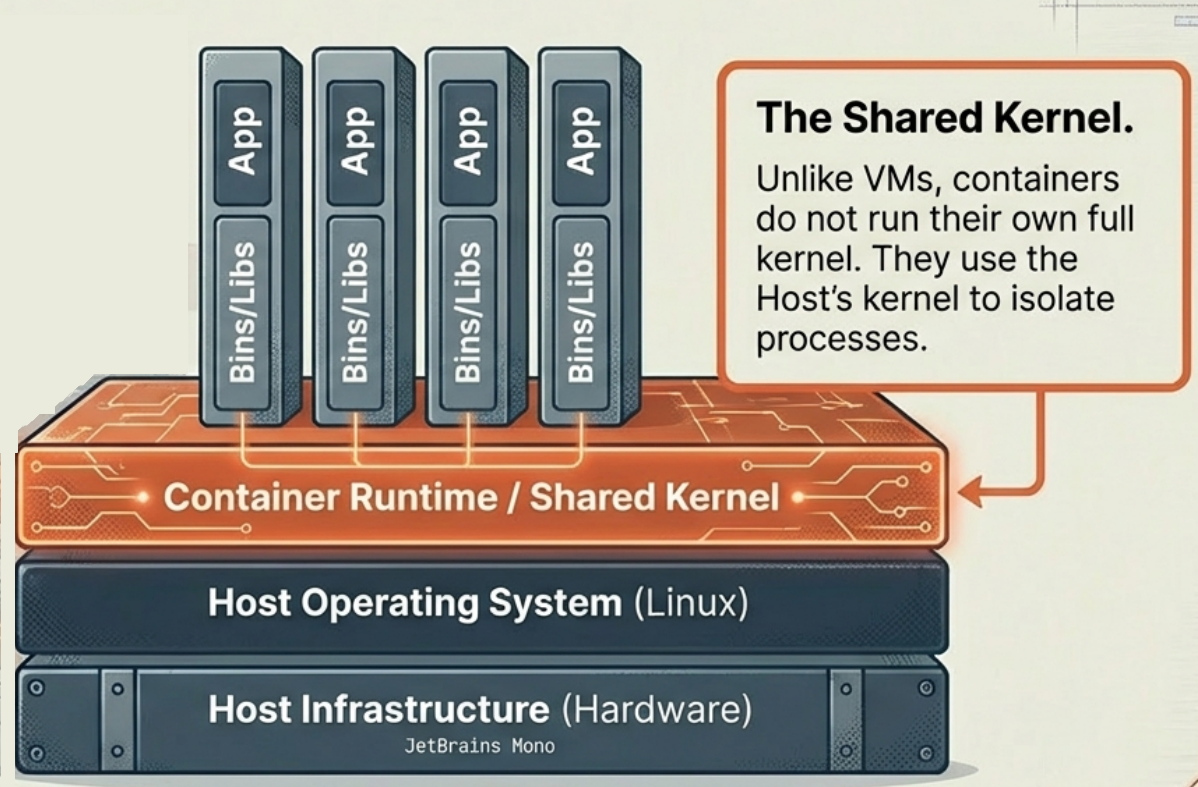
Section titled “How Containers Work”- Shared OS Kernel: Unlike virtual machines (VMs) that require a full guest operating system, containers share the host system’s operating system kernel as a read-only resource.
- Architectural Layers: The typical container architecture consists of several layers:
- Physical Infrastructure: The underlying hardware (CPU, disk storage, network).
- Host OS and Kernel: Acts as the bridge between hardware and software.
- Container Engine: Sits on top of the host OS to manage containers (e.g., Docker).
- Applications and Binaries: The very top layer where isolated user spaces run the applications and their necessary libraries.
- Technological Origins: Containerization evolved from Linux cgroups (control groups), a feature used to isolate and control resource usage (like CPU and RAM) for OS processes. This later evolved into Linux Containers (LXC) and became mainstream with the launch of Docker in 2013.
Key Advantages
Section titled “Key Advantages”- Low Resource Overhead: Because containers share the host OS and skip running an entire guest OS, they are significantly more lightweight and consume far less CPU, RAM, and storage than VMs.
- Rapid Startup and Deployment: Containers start up almost instantly because there is no operating system to boot. This allows them to be spun up, torn down, and restarted incredibly fast.
- High Portability: Since a container packages the app and all its dependencies into a single unit, it behaves the same way across any system running a compatible container engine, whether in development, staging, or production.
- Immutability: Containers support immutable infrastructure, meaning a container never changes after it is deployed; if an update is needed, the old container is replaced with a newly built one.
Limitations and Drawbacks
Section titled “Limitations and Drawbacks”- Weaker Security Isolation: While containers are isolated from each other, they share the host system’s OS kernel. If a security vulnerability compromises the shared kernel, it could potentially affect all containers running on that host.
- Strict OS Compatibility: Containers must run on an operating system that is the same or very similar to the host OS. If an application requires a completely different OS, it needs a different host entirely.
- Storage Complexity: Containers are ephemeral, meaning they start and stop automatically and their internal data is lost when they shut down. To retain data, you must configure persistent external storage solutions, which can add complexity.
Primary Use Cases
Section titled “Primary Use Cases”- Microservices Architectures: Containers are the ideal fit for microservices, where large applications are broken down into small, independent services. Containers provide a standardized, isolated environment for each service, ensuring they run consistently without conflicts.
- CI/CD (Continuous Integration/Continuous Deployment): Containers provide a highly consistent environment for testing code. They ensure that tests are reliable and repeatable, allowing developers to automate deployments and release higher-quality software much faster.
- PaaS (Platform as a Service) Scenarios: Containerization allows cloud providers to efficiently host multiple developer environments on the same infrastructure, delivering standardized platforms for developers to build and deploy applications.
Popular container providers
Section titled “Popular container providers”- Docker Docker is the most popular and widely used container runtime. Docker Hub is a giant public repository of popular containerized software applications. Containers on Docker Hub can instantly downloaded and deployed to a local Docker runtime.
- RKT Pronounced “Rocket”, RKT is a security-first focused container system. RKT containers do not allow insecure container functionality unless the user explicitly enables insecure features. RKT containers aim to address the underlying cross contamination exploitive security issues that other container runtime systems suffer from.
- Linux Containers (LXC) The Linux Containers project is an open-source Linux container runtime system. LXC is used to isolate operating, system-level processes from each other. Docker actually uses LXC behind the scenes. Linux Containers aim to offer a vender neutral open-source container runtime.
- CRI-O CRI-O is an implementation of the Kubernetes Container Runtime Interface (CRI) that allows the use of Open Container Initiative (OCI) compatible runtimes. It is a lightweight alternative to using Docker as the runtime for Kubernetes.
